XDR Explained: Extended Detection and Response Guide
What Security Operations Teams Need
Security operations teams face three fundamental challenges: getting a correlated view of alerts across their environment, working with speed, accuracy, and confidence, and remediating threats with guidance and automated playbooks. XDR — Extended Detection and Response — is the platform category designed to solve all three.

Why Traditional Approaches Fall Short
Ransomware Campaigns Are Multi-Vector
Modern attacks don’t come from a single direction. A well-tailored phishing email leads a user to a malicious website. That website drops a payload onto the user’s device. The malware then moves laterally to other machines and eventually exfiltrates or encrypts data. Each stage of this kill chain may touch a different security tool — email gateway, DNS security, endpoint protection, network firewall, and data loss prevention.
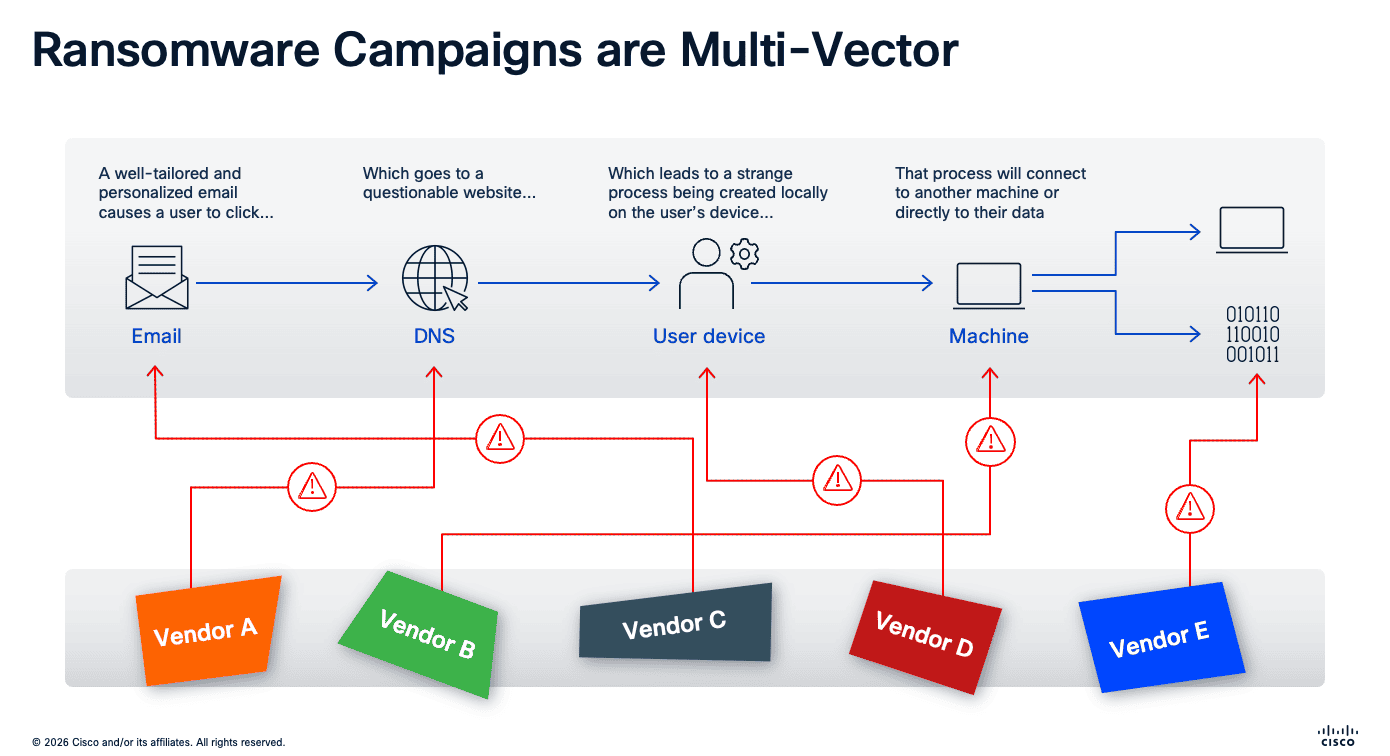
When each of these tools is managed by a different vendor with its own console, alerts become fragmented. No single product sees the full attack story. This is the fundamental gap that XDR closes.
What Is XDR?
Extended Detection and Response (XDR) is a security platform that collects and correlates data across multiple security layers — endpoints, network, cloud, and email — to detect threats faster and respond more effectively than siloed tools.
Unlike traditional SIEM solutions that rely on log aggregation and manual correlation, XDR uses advanced analytics and automation to connect the dots across your security stack and surface the incidents that matter.
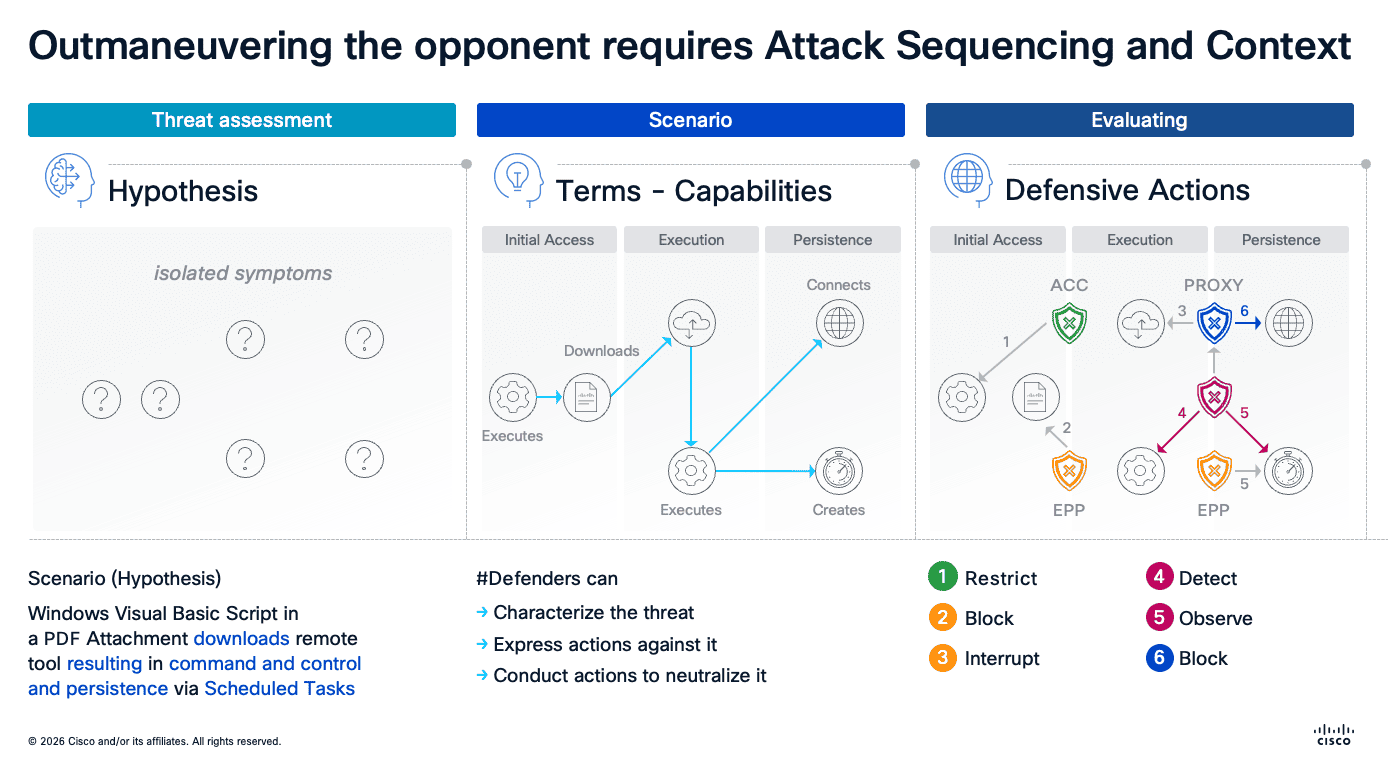
Attack Sequencing and Context
Effective security operations requires outmaneuvering the adversary through three key capabilities:
- Threat Assessment (Hypothesis): Forming a hypothesis about what’s happening based on isolated symptoms — for example, a Windows Visual Basic Script in a PDF attachment downloading a remote tool that establishes command and control via scheduled tasks
- Scenario Modeling (Capabilities): Defenders characterize the threat across initial access, execution, and persistence stages, then express and conduct actions to neutralize it
- Evaluating Defensive Actions: Mapping specific actions — restrict, block, interrupt, detect, observe — to each stage of the attack lifecycle
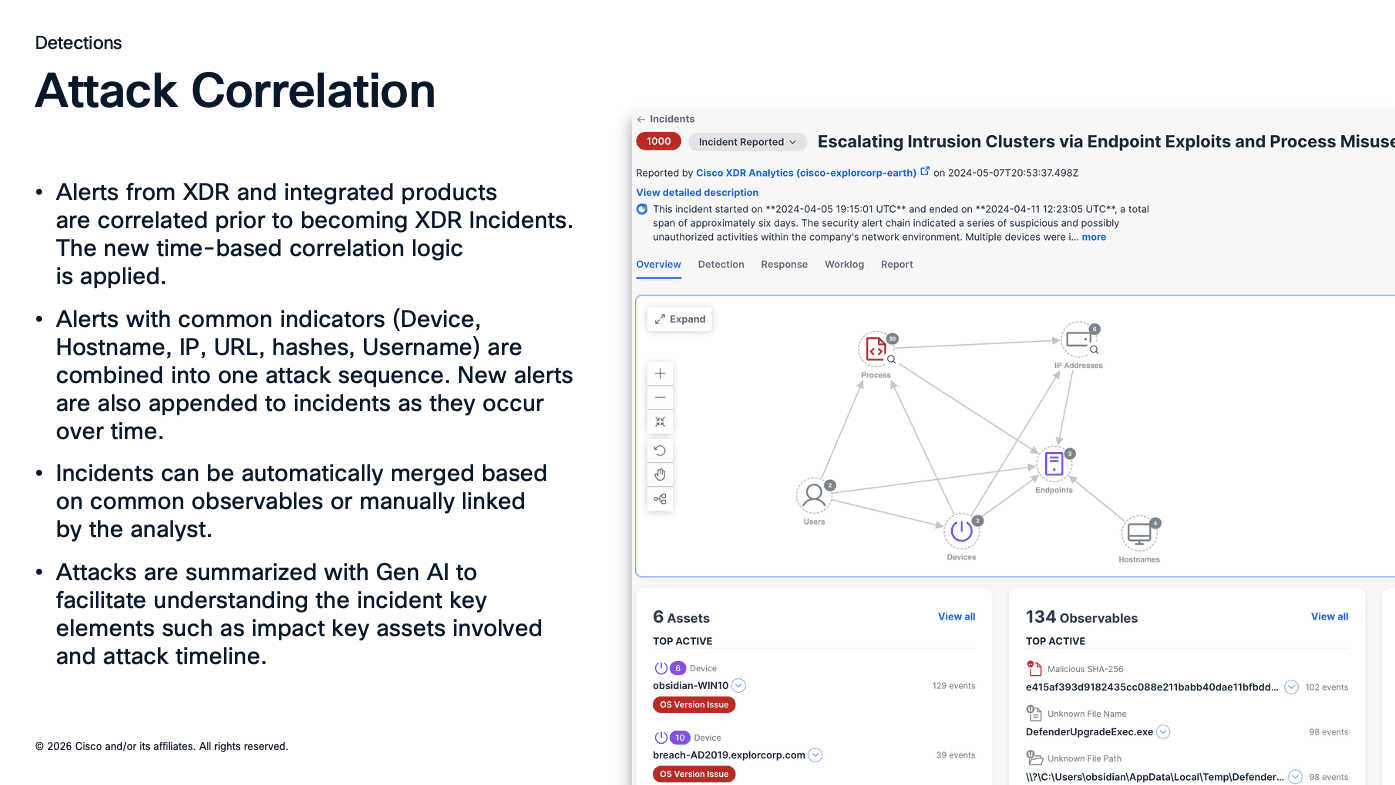
How Cisco XDR Correlates Attacks
Alerts from XDR and integrated products are correlated before becoming XDR Incidents. The platform uses time-based correlation logic to combine alerts with common indicators — device, hostname, IP, URL, hashes, and username — into a single attack sequence. New alerts are appended to incidents as they occur over time.
Incidents can be automatically merged based on common observables or manually linked by the analyst. Attacks are summarized with Gen AI to help analysts understand the incident’s key elements, including impacted assets and attack timeline.
Cisco XDR Architecture
Data Sources and Integrations
Cisco XDR takes an open ecosystem approach, integrating with both native Cisco products and third-party tools across the entire security stack.
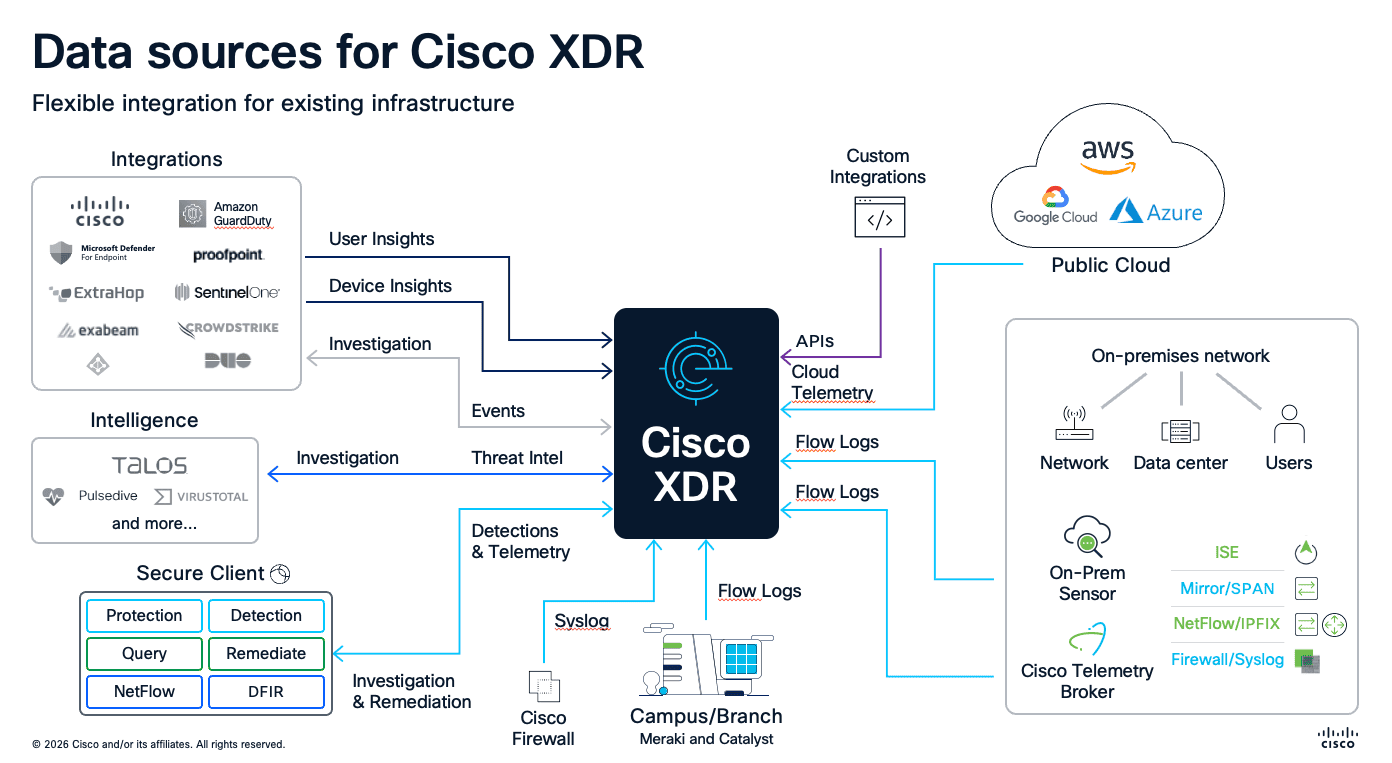
Native integrations include:
- Cisco Secure Endpoint — endpoint detection and response
- Cisco Secure Firewall — network traffic and intrusion events
- Cisco Secure Email — email threat intelligence
- Cisco Umbrella (DNS) — DNS and web security events
- Cisco Secure Access — ZTNA and SSE
- Meraki SM — network device management
- Cisco Secure Client — unified agent telemetry
Third-party integrations include:
- CrowdStrike, SentinelOne, Microsoft Defender for Endpoint
- Proofpoint, ExtraHop, Exabeam
- Splunk, VirusTotal, and many more
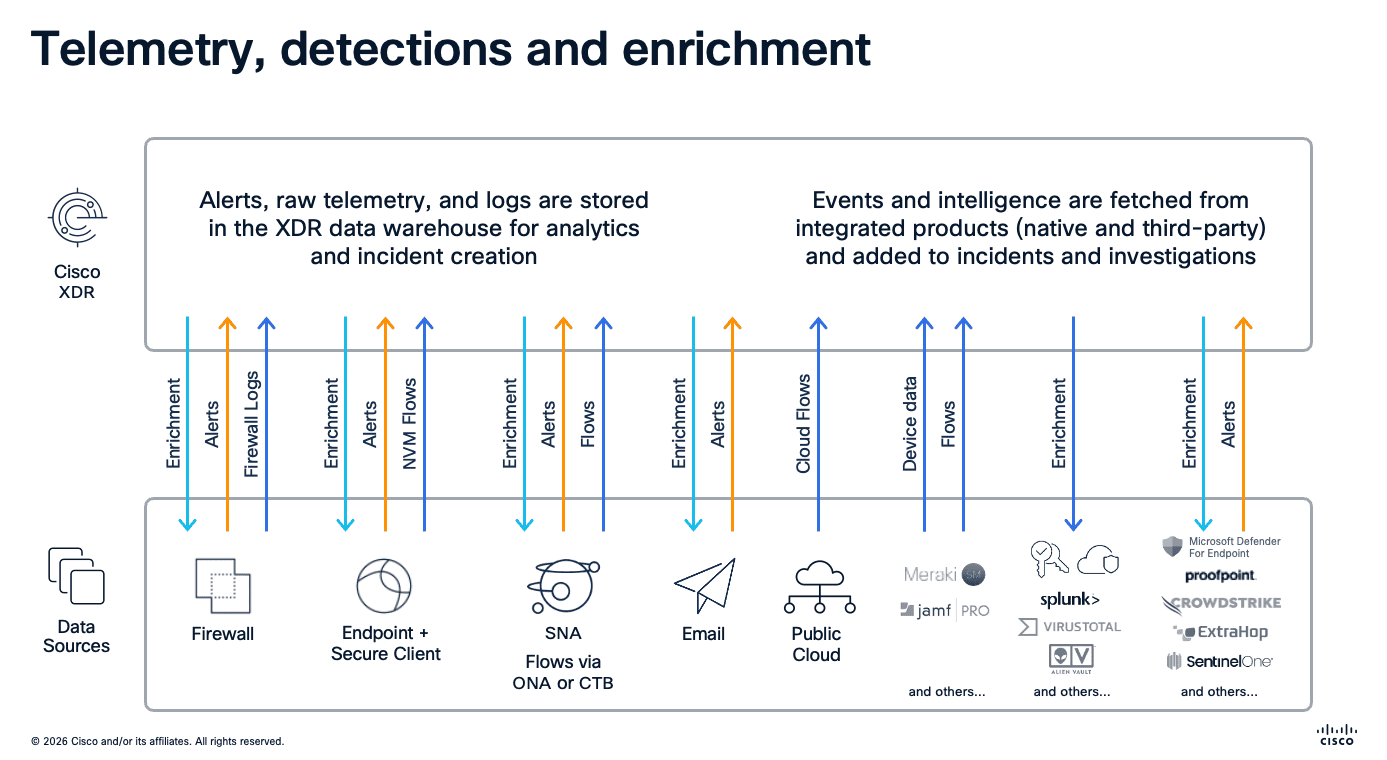
Telemetry, Detections, and Enrichment
Alerts, raw telemetry, and logs from every data source — firewall, endpoint, SNA (Secure Network Analytics), email, and public cloud — are stored in the XDR data warehouse for analytics and incident creation. Simultaneously, events and intelligence are fetched from integrated products (both native and third-party) and added to incidents and investigations through enrichment.
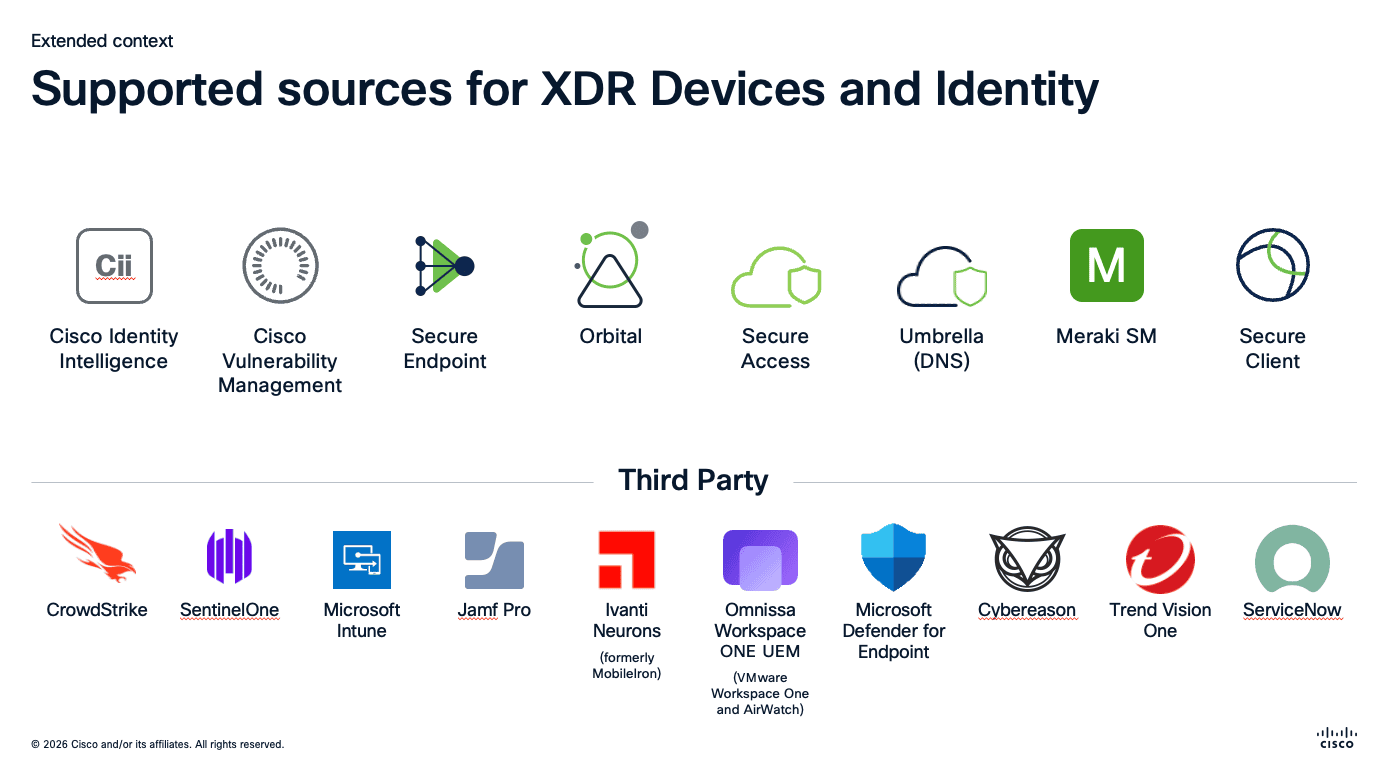
Supported Sources for Devices and Identity
For device and identity context, Cisco XDR pulls from a wide range of sources:
Cisco native: Cisco Identity Intelligence, Cisco Vulnerability Management, Secure Endpoint, Orbital, Secure Access, Umbrella (DNS), Meraki SM, and Secure Client.
Third-party: CrowdStrike, SentinelOne, Microsoft Intune, Jamf Pro, Ivanti Neurons, Omnissa Workspace ONE UEM, Microsoft Defender for Endpoint, Cybereason, Trend Vision One, and ServiceNow.
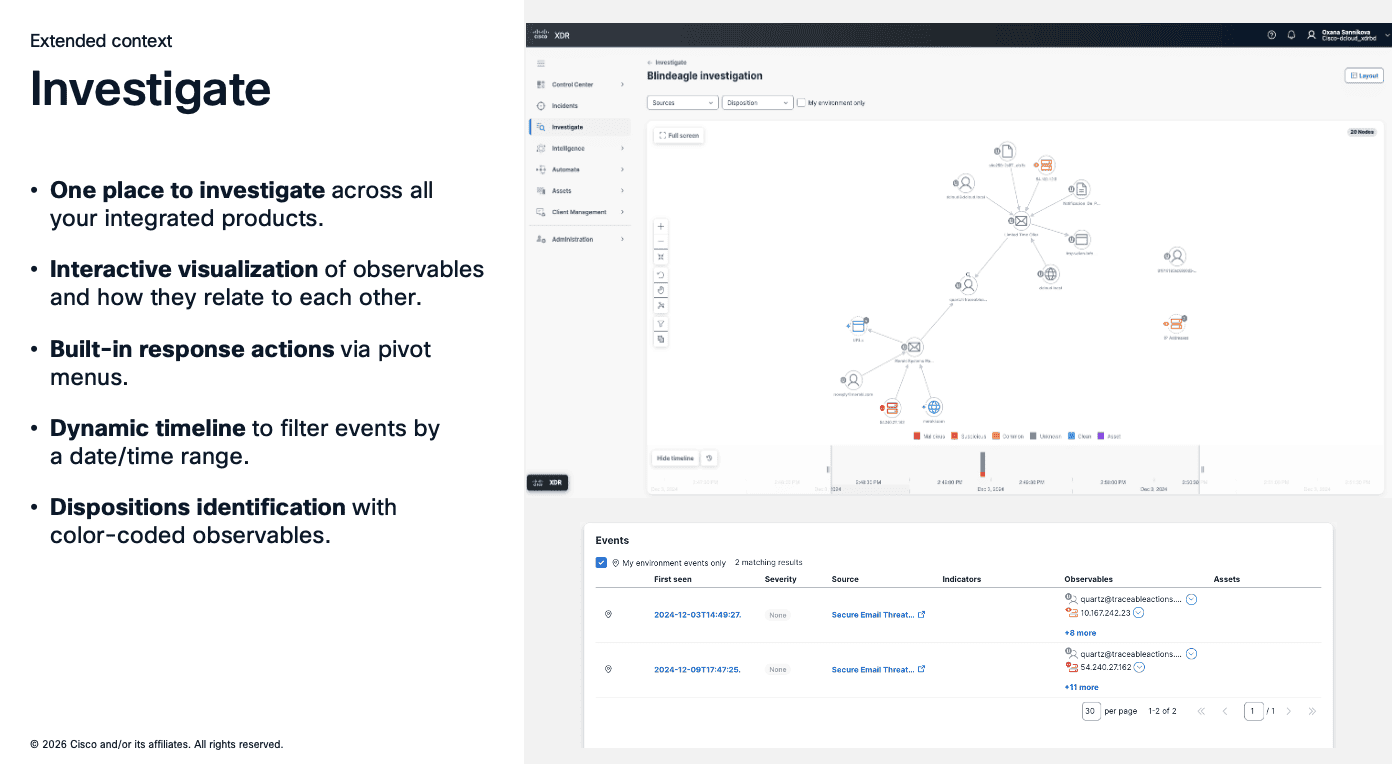
Investigations in Cisco XDR
The investigation experience in Cisco XDR provides three key capabilities:
- Interactive Graph: Displays and groups the entities involved in the incident, showing relationships between users, devices, IP addresses, domains, files, and more
- Graph Filter: Flexible filter options to highlight or hide different node types and relationship types, letting analysts focus on what matters
- Timeline: An interactive timeline of events that lets analysts view specific periods of time and understand the sequence of an attack
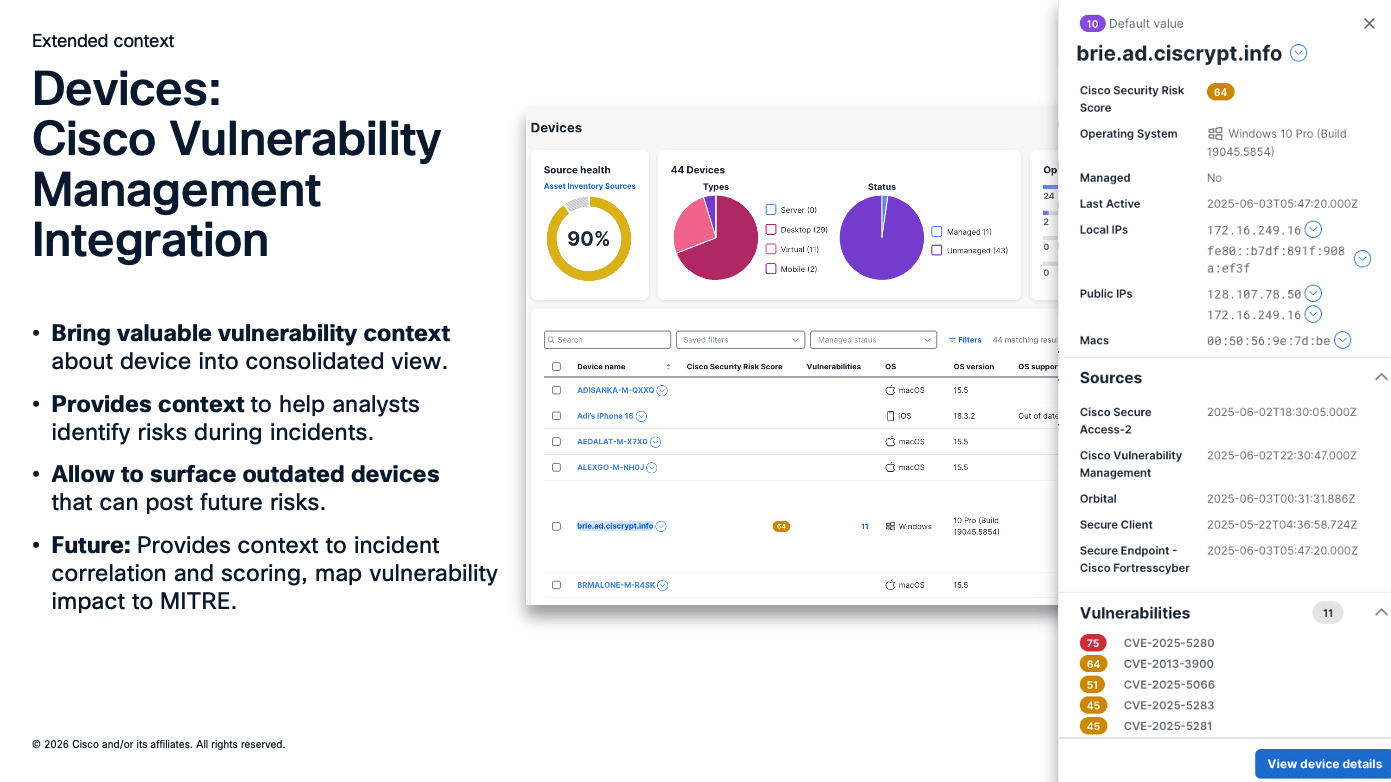
Device Context and Vulnerability Management
Cisco XDR integrates with Cisco Vulnerability Management to bring valuable device context into a consolidated view. This integration:
- Provides context to help analysts identify risks during incidents
- Surfaces outdated devices that can pose future risks
- Displays Cisco Security Risk Scores alongside vulnerability data and CVEs
- Maps vulnerability impact to the MITRE ATT&CK framework for incident correlation and scoring
Incident Details Through Progressive Disclosure
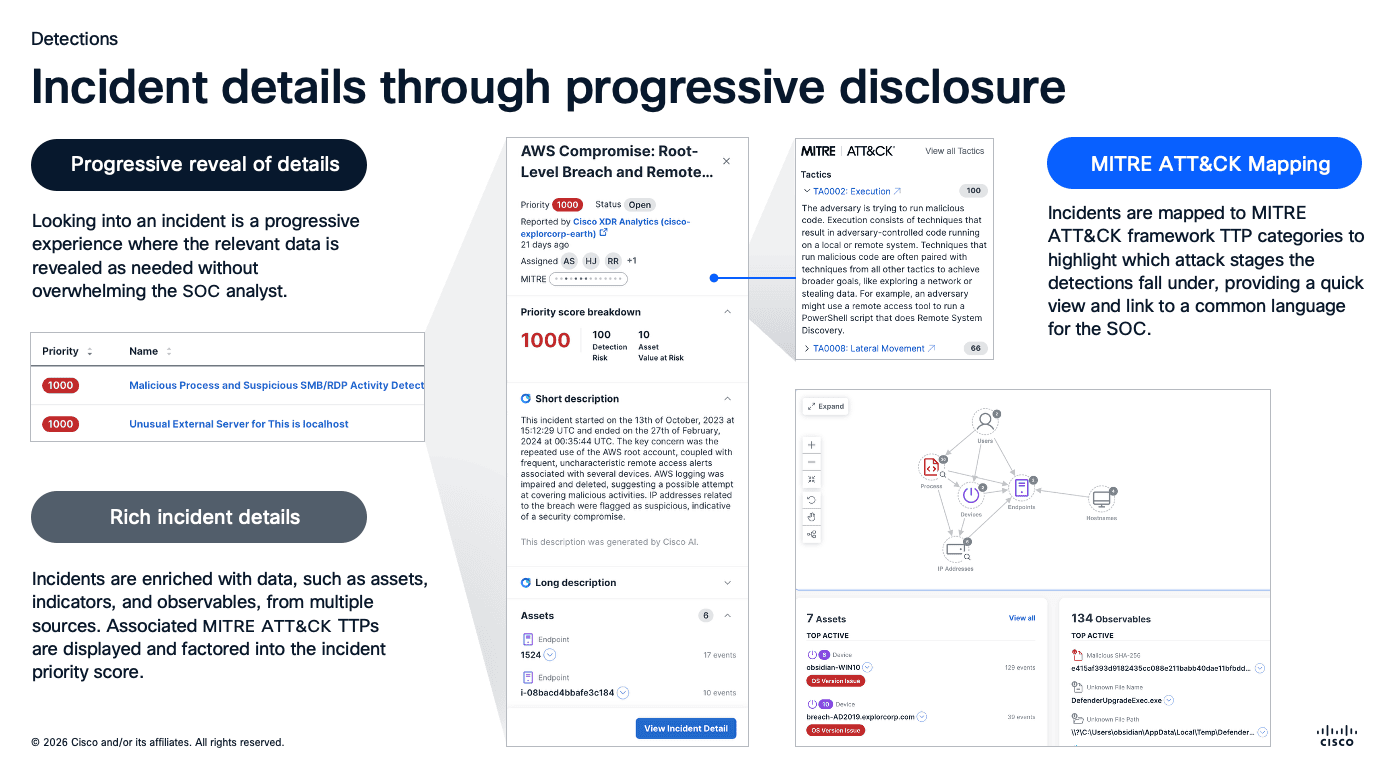
Looking into an incident in Cisco XDR is a progressive experience where relevant data is revealed as needed without overwhelming the SOC analyst.
Progressive Reveal of Details
Incidents surface priority scores, AI-generated descriptions, assigned analysts, and high-level timeline information at a glance. Drilling in reveals assets, indicators, observables, and the complete attack graph.
MITRE ATT&CK Mapping
Incidents are mapped to MITRE ATT&CK framework TTP categories to highlight which attack stages the detections fall under, providing a common language for the SOC.
Rich Incident Details
Incidents are enriched with data — assets, indicators, and observables — from multiple sources. Associated MITRE ATT&CK TTPs are displayed and factored into the incident priority score.
XDR vs. SIEM vs. EDR
| Capability | EDR | SIEM | XDR |
|---|---|---|---|
| Scope | Endpoints only | Log aggregation | Cross-domain |
| Detection | Endpoint-focused | Rule-based | AI-driven correlation |
| Response | Endpoint actions | Manual | Automated cross-domain |
| Integration | Limited | Broad but manual | Native + third-party |
| Complexity | Low | High | Medium |
Getting Started with XDR
- Audit your current stack — identify what telemetry sources you already have
- Start with what you have — connect your existing Cisco (or third-party) tools to XDR
- Focus on high-value use cases — ransomware detection, compromised credentials, data exfiltration
- Build response playbooks — automate common response actions
- Measure and iterate — track mean time to detect (MTTD) and mean time to respond (MTTR)
Frequently Asked Questions
What is XDR in cybersecurity? XDR (Extended Detection and Response) is a security platform that collects and correlates data across multiple security layers including endpoints, network, cloud, and email to detect threats faster and respond more effectively than siloed tools like standalone EDR or SIEM.
How does Cisco XDR work? Cisco XDR integrates with both native Cisco products and third-party tools to collect alerts and telemetry. It uses time-based correlation logic to combine alerts with common indicators such as device, hostname, IP, URL, and username into unified attack sequences, then uses AI to summarize incidents for analysts.
What is the difference between XDR, SIEM, and EDR? EDR focuses only on endpoints with endpoint-specific actions. SIEM aggregates logs broadly but relies on manual, rule-based correlation. XDR provides AI-driven cross-domain detection and automated response across endpoints, network, cloud, and email with both native and third-party integrations.
What data sources does Cisco XDR integrate with? Cisco XDR integrates with native products like Secure Endpoint, Secure Firewall, Secure Email, Umbrella DNS, Secure Access, and Meraki SM. It also supports third-party tools including CrowdStrike, SentinelOne, Microsoft Defender, Proofpoint, Splunk, and many more.
How do I get started with XDR? Start by auditing your current security stack to identify existing telemetry sources. Connect your Cisco or third-party tools to XDR, focus on high-value use cases like ransomware detection, build automated response playbooks, and measure improvements in mean time to detect and respond.
Related Guides
Looking to deepen your security knowledge? Explore our other comprehensive guides:
- Zero Trust Security: The Complete Guide — Understand the Zero Trust framework and how continuous verification, micro-segmentation, and ZTNA work alongside XDR to protect your organization.
- Cisco Firewall Guide: From ASA to FTD — Learn how Cisco Secure Firewall integrates with XDR as a key telemetry source for network traffic and intrusion events.
Related Episodes
Episodes & Posts on This Topic
MITRE ATT&CK Framework Explained: A Practical Guide for Security Teams
Learn how the MITRE ATT&CK framework maps adversary tactics and techniques. Practical guide for using ATT&CK with Cisco XDR, threat hunting, and incident …
XDR Integration: Cisco's Open Ecosystem Approach
How Cisco XDR uses open ecosystem integrations and cross-domain threat correlation to simplify detection and automate incident response.
Firewall Evolution: Cisco's PIX to FTD Journey Explained
Explore Cisco's firewall evolution from PIX to ASA to FTD, including Encrypted Visibility Engine, identity-based policies, and modern deployment strategies.
